For years, the advice has been simple:
Turn on Multi-Factor Authentication (MFA) and you’ll be safe.
And to be clear, MFA is essential. If it isn’t enabled across your business, that is the first thing to fix.
But here’s the uncomfortable truth:
…MFA is no longer the finish line.
Attackers have evolved. They are no longer just trying to guess passwords. They are targeting something far more valuable: your identity.
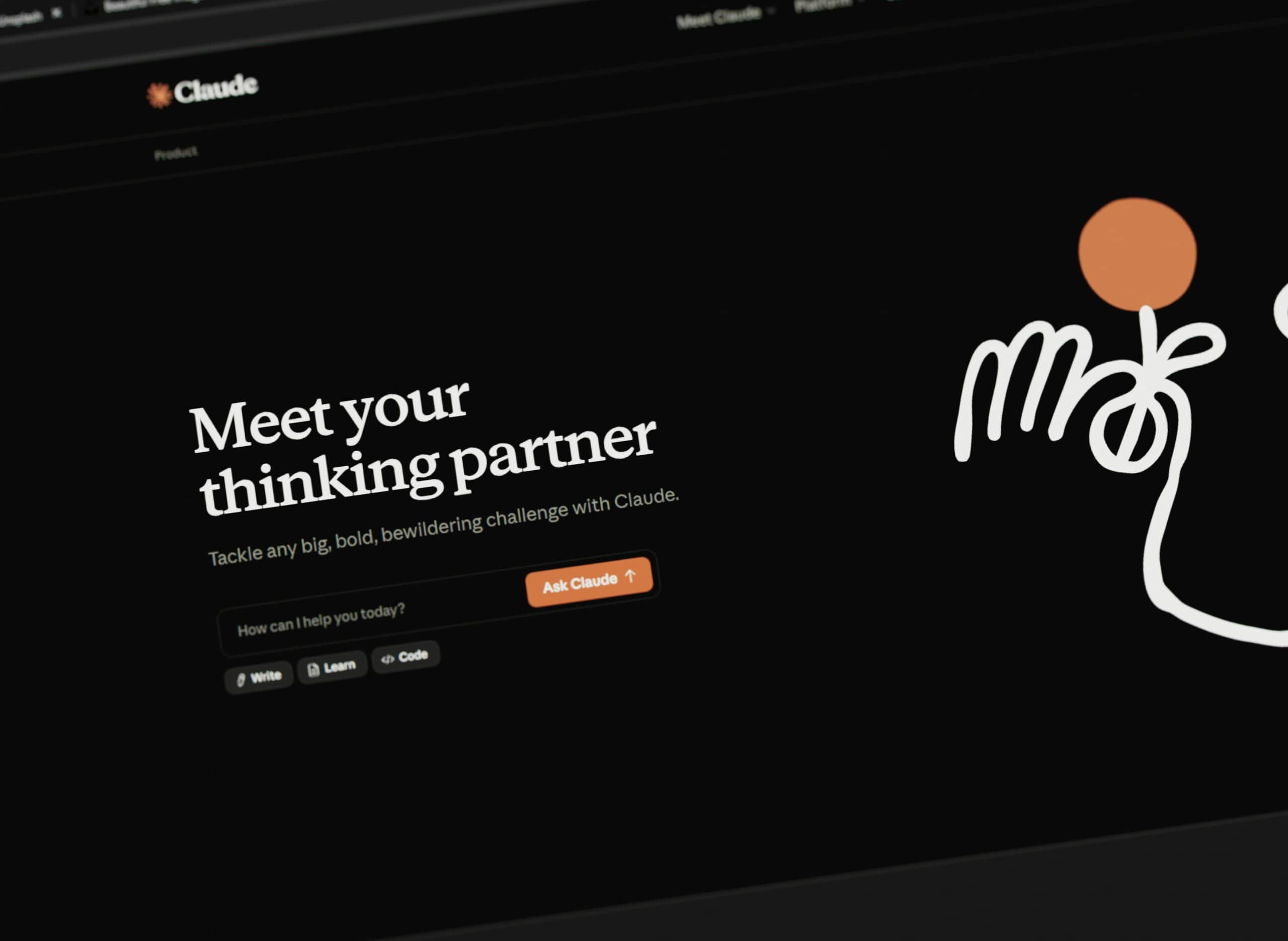
Whether you use Microsoft 365 or Google Workspace, your business now runs on identity. Email, files, Teams, SharePoint, Google Drive, internal chat, third-party SaaS apps. Everything ties back to user authentication.
So what happens when attackers stop attacking the password and start attacking the session?
Login Is No Longer the Only Door
Most people think security happens at the login screen.
- You enter your password.
- You approve the MFA prompt.
- You’re in.
The assumption is simple: if MFA was approved, the login must be legitimate.
But many modern attacks happen after that moment.
When you log in successfully, your system creates a session token. Think of it as a digital pass that confirms you are authenticated. Your browser uses that token so you don’t have to re-enter your password on every click.
If an attacker steals that token, they do not need your password.
They do not need your MFA code. They simply reuse your authenticated session. From the system’s perspective, it looks exactly like you.
How MFA Gets Bypassed in the Real World
This is not theory. These techniques are actively used in identity-based attacks today.
One method uses phishing pages that act as a live proxy between you and the real Microsoft or Google login portal. You enter your credentials. You approve the MFA prompt. Everything appears normal.
Behind the scenes, the attacker captures your session token.
You log in successfully. They log in successfully.
Another increasingly common method involves infostealer malware. These tools extract browser cookies and session data from infected machines. No password cracking. No brute force. Just reuse of a legitimate session.
The key point is this:
MFA protects the authentication step. It does not automatically protect the authenticated session.
Why This Matters for Microsoft 365 and Google Workspace
Both Microsoft 365 and Google Workspace are identity-first ecosystems.
If an attacker compromises a user identity, they do not just gain access to email.
They may gain access to:
- SharePoint or Google Drive data
- Teams or Google Chat conversations
- Financial documents
- HR records
- CRM integrations
- Admin portals
- Connected third-party SaaS platforms
In many businesses, a single compromised identity becomes the master key to the entire organisation.
And because the login was technically successful, traditional security controls often do not trigger alerts.
That is the gap.
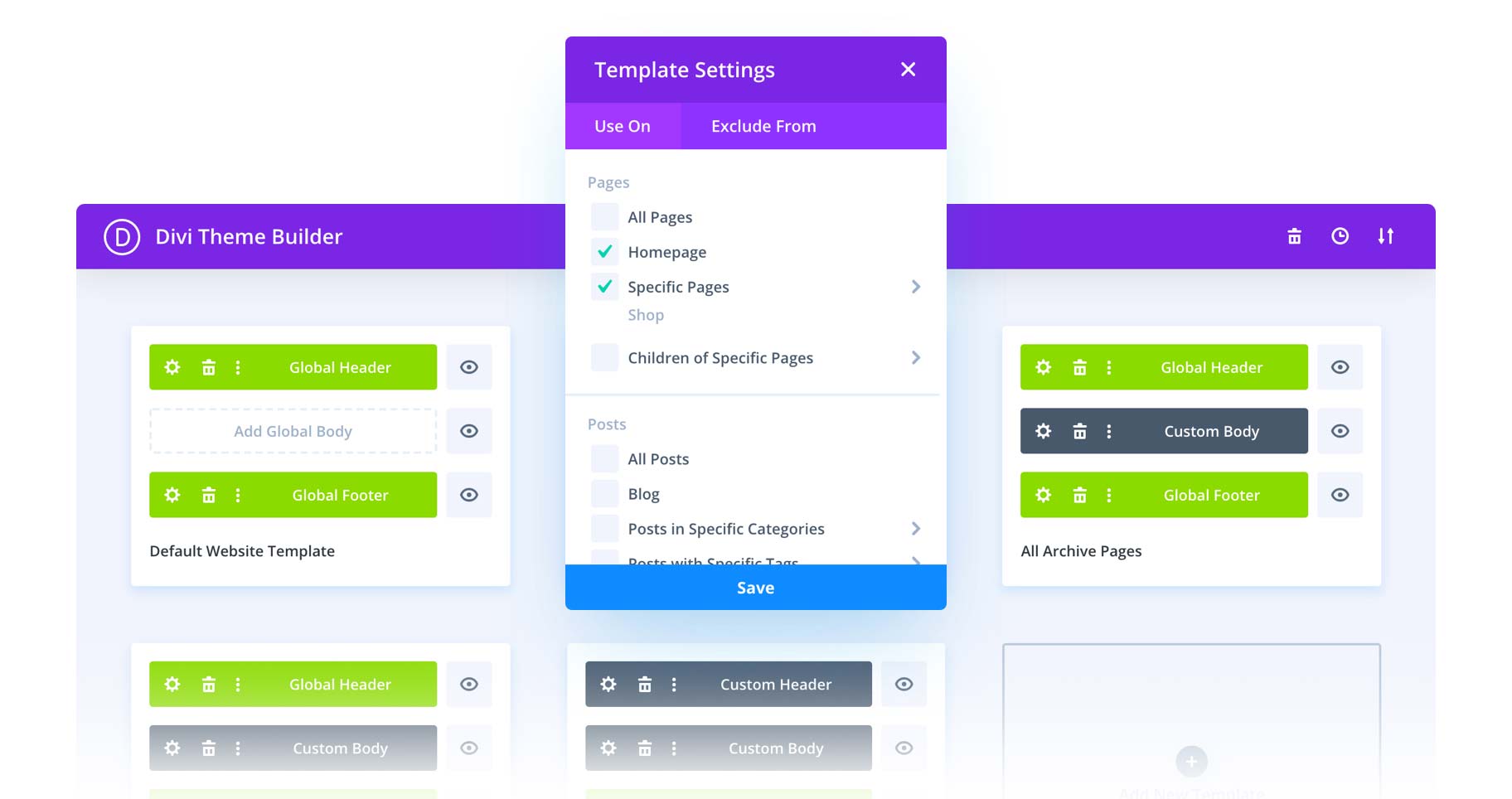
The Next Layer: Identity Threat Detection and Response (ITDR)
This is where Identity Threat Detection and Response comes in.
ITDR does not just ask, “Did the login succeed?”
- It asks smarter questions:
- Is this identity behaving normally?
- Is this session being reused from a different device or location?
- Has privilege suddenly changed?
- Is sensitive data being accessed unusually?
- Is lateral movement happening inside the tenant?
ITDR assumes credentials can be compromised, even with MFA enabled. It focuses on detecting suspicious identity behaviour after authentication.
It is a shift in thinking.
Instead of only protecting the front door, you monitor what happens inside the building.
MFA Is Baseline. Not Advanced.
Five years ago, enabling MFA was considered advanced security.
Today, it is the minimum standard.
Real protection now involves layers:
- Phishing-resistant MFA methods
- Conditional Access or contextual access controls
- Endpoint Detection and Response
- Security Awareness Training
- Identity-level monitoring through ITDR
Because attackers do not stop at login, and neither should your security strategy.
We Protect Identity, Not Just Devices
At Razz Hosting, we have expanded our security stack to include Identity Threat Detection and Response (ITDR) for both Microsoft 365 and Google Workspace environments through our Complete Business Essentials plan.
That means we monitor identity behaviour, session anomalies, privilege abuse, and suspicious activity inside your tenant, not just login attempts.
It is protection designed for how attacks actually happen today.
Final Thought
If your security conversation ends with “we’ve turned on MFA,” you are protecting the front door, which is great, but modern identity attacks have ways around that locked door.
The real question is not just:
Can someone log in?
It is:
If they do, would you know?