EDR, ITDR, SAT… Oh My!
If you have looked into cyber security recently, you have probably come across a wave of acronyms.
EDR.
ITDR.
SAT.
For most business owners, it quickly becomes overwhelming.
You are trying to run a business. You are not trying to decode security terminology!
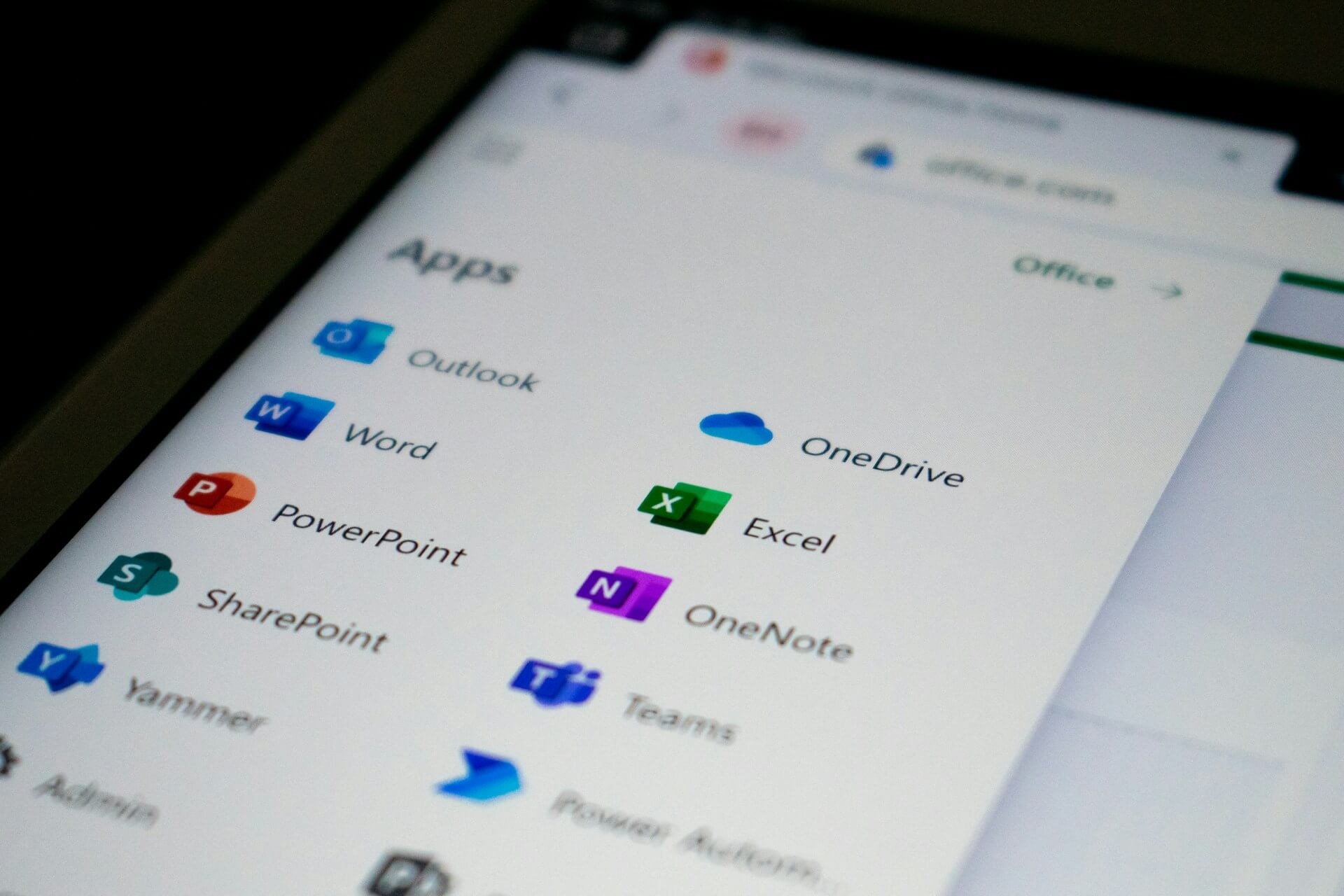
At the same time, you know the risks are real. Data breaches are no longer something that only affects large corporations. Small and medium Australian businesses are increasingly targeted, especially those using Microsoft 365 and handling sensitive client information.
So let’s slow it down and make sense of it.
The Problem Has Changed
There was a time when installing antivirus software felt sufficient, or even the stock standard antivirus that shipped with your computer.
Today, cyber threats look very different.
Attackers do not just try to infect computers. Increasingly, they try to log in using stolen credentials. They exploit human behaviour. They move quietly rather than loudly.
If your business relies on Microsoft 365 for email, file storage and collaboration, identity-based attacks are now one of your biggest risks.
That is why modern security is built in layers.
Layer One: Protecting the Device
Endpoint Detection and Response, or EDR, focuses on protecting the actual computer or laptop.
Traditional antivirus primarily relies on known threat signatures. That means it is very effective against yesterday’s malware, but not always against new or modified attacks.
EDR works differently. It continuously monitors device behaviour in real time. Instead of only asking “Is this file known to be malicious?”, it asks “Is this behaviour normal?”
It looks for:
- Ransomware patterns such as mass file encryption
- Suspicious PowerShell or command line activity
- Unusual privilege escalation
- Processes attempting to disable security controls
If something abnormal occurs, it does not simply record it. It can isolate the device, terminate malicious processes and trigger investigation.
For businesses handling sensitive client data, even a single compromised laptop can become the entry point to your broader Microsoft 365 environment.
EDR reduces the likelihood that one infected device turns into a full-scale incident.
Layer Two: Protecting the Identity
The second layer is Identity Threat Detection and Response, or ITDR.
This is where things have shifted significantly in recent years.
If someone gains access to a Microsoft 365 account, they may not need malware at all. With valid credentials, they can read emails, impersonate staff, reset passwords and access confidential files.
Many business owners assume that enabling Multi Factor Authentication solves the problem completely. MFA is essential, but it is not bulletproof.
Modern attackers use techniques such as session hijacking and token theft. Instead of stealing a password, they capture an authenticated session after a user has already logged in. From the system’s perspective, the activity can look legitimate.
That means compromise does not always happen because someone guessed a password. It can happen because a session was intercepted or a login token was abused.
For businesses in finance, mortgage broking, accounting, legal and other professional services, the consequences are serious. A compromised account may expose tax file numbers, financial statements, loan applications, identification documents or sensitive client correspondence.
In these industries, the damage is not just technical. It is reputational. Clients trust you with highly confidential information and assume appropriate safeguards are in place.
ITDR monitors identity activity inside Microsoft 365. It looks for unusual behaviour patterns, impossible travel logins, suspicious administrative changes and privilege escalation. It is designed to detect when something is not normal, even if the login appears valid.
Your email account is often the master key to your organisation. Protecting it is no longer optional, particularly when client data sits behind that login.
Layer Three: Protecting the Human
Even with strong device and identity protection, people remain part of the equation.
Most cyber incidents begin with a human interaction. A phishing email that looks genuine. A fake Microsoft 365 login page. A message that appears to come from a trusted contact.
Attackers study behaviour. They imitate suppliers. They mimic internal email styles. They create urgency.
Security Awareness Training helps staff recognise these tactics in the real world. Not through a once-a-year compliance module, but through ongoing, relevant education that evolves with current threats.
It builds:
- Awareness of phishing and credential harvesting
- Understanding of business email compromise
- Confidence in reporting suspicious activity
- Better password and authentication habits
The goal is not to turn staff into security experts.
It is to make suspicious activity feel familiar rather than surprising.
When employees understand what modern attacks look like, technology has a much stronger chance of doing its job effectively.
Why This Matters for Australian Businesses
Small and medium businesses are attractive targets.
They hold valuable data. They rely heavily on cloud systems. And they often lack the internal resources of larger enterprises.
Regulatory expectations around data protection are also increasing. Clients assume you are protecting their information responsibly.
Layered security is no longer a luxury upgrade. It is part of running a professional, modern business.
Making It Practical
For most business owners, the challenge is not whether security matters. It is understanding what is genuinely necessary and what is simply noise.
You do not need to master the technical details behind endpoint monitoring or identity detection.
You simply need confidence that the right protections are in place for your business.
That is why at Razz Hosting, layered protection is built into our Complete Business Essentials managed IT service.
It includes 24/7 monitored Endpoint Detection and Response and Microsoft 365 identity threat detection, powered by leading global security platform Huntress.
You do not need to compare vendors or choose between tiers. You simply need confidence that the right protections are in place.
Because security should not sit in the background as a constant worry. It should simply be handled.
Final Thoughts
- EDR protects the device.
- ITDR protects the identity.
- SAT protects the human.
Together, they form a practical, layered defence for modern businesses using Microsoft 365.
If you would like to understand what that looks like for your organisation, the Razz Hosting team is always happy to talk it through in plain English.